Summary
Assigned CVE: CVE-2020-4485 and CVE-2020-4486 have been assigned and RedyOps Labs has been publicly acknowledged by the vendor.
Known to Neurosoft’s RedyOps Labs since: 13/05/2020
Exploit Code: N/A
Vendor’s Advisory: https://www.ibm.com/support/pages/node/6257885
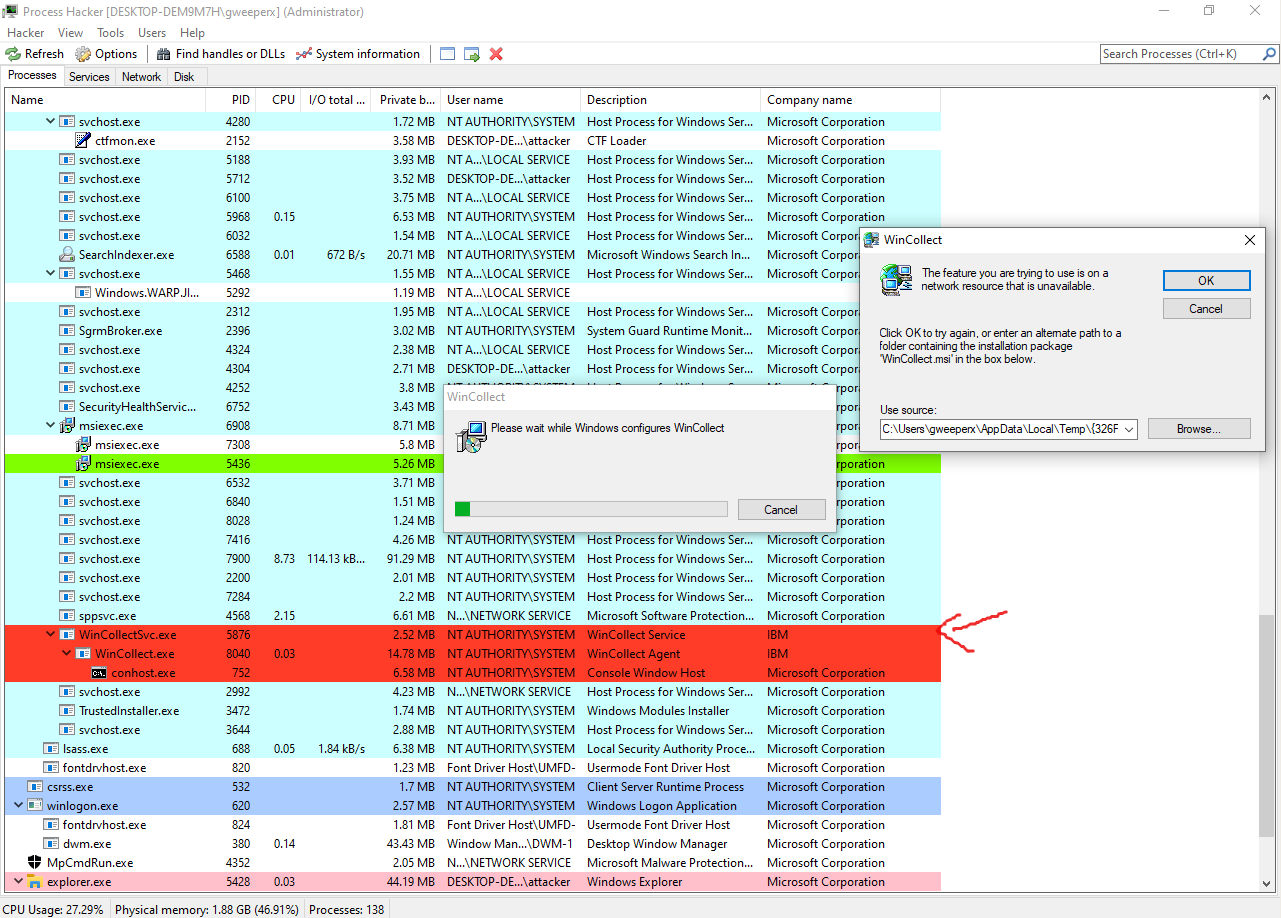
An Elevation of Privilege (EoP) exists in IBM QRadar Wincollect 7.2.0 – 7.2.9 . The vulnerability described gives the ability to a low privileged user to delete any file from the System and disable the Wincollect service. This arbitrary delete vulnerability can be leveraged in order to gain access as NT AUTHORITY\SYSTEM. During the exploitation, the attacker disables the Wincollect service.
Description
There are two distinct root causes which can lead to the same issue (arbitrary delete):
After the installation of the WinCollect, the installer remains under the folder c:\Windows\Installer . Any user with low privileges can run the installer with the following command:
msiexec /fa c:\Windows\Installer****.msiThe WinCollect’s installer, although it will eventually fail when executed by a low privileged user, it will create log files under the User’s Temp folder.
At some point, the installer will try to delete those log files as SYSTEM. As long as the user controls the files in his Temp folder (C:\Users\username\AppData\Local\Temp), they can create a symlink targeting any file in the system. When the installer tries to delete these files, it will follow the symlink and will perform the delete actions as SYSTEM.
Even if the symlinks are mitigated in the future by Microsoft, an attacker can achieve the arbitrary delete by editing the file ~xxxx.tmp .
The file C:\Users\username\AppData\Local\Temp\~xxxx.tmp where xxxx is a random hex, ends with the lines:
[SearchRepalceTargetBackupFiles]
C:\Program Files\IBM\WinCollect\config\CmdLine.txt=C:\Users\attacker\AppData\Local\Temp_isFD30
C:\Program Files\IBM\WinCollect\config\logconfig_template.xml=C:\Users\attacker\AppData\Local\Temp_isFD8F
C:\Program Files\IBM\WinCollect\templates\tmplt_AgentCore.xml=C:\Users\attacker\AppData\Local\Temp_isFDAFAn attacker can edit these lines and add the files he wants to delete. For example:
[SearchRepalceTargetBackupFiles]
C:\Program Files\IBM\WinCollect\config\CmdLine.txt=C:\windows\win.ini
C:\Program Files\IBM\WinCollect\config\logconfig_template.xml=C:\Users\Admin\whatever.exe
C:\Program Files\IBM\WinCollect\templates\tmplt_AgentCore.xml=C:\Users\anotheruser\logs.txtWhen we cancel the installer, these files will be deleted as SYSTEM.
As a bonus, during this process, the wincollect service will stop and will remain stopped, until we cancel the operation.
Exploitation
In order to Exploit the issue, no special program is needed .
In the following paragraph, a step by step explanation of the Video PoC is provided.
Please note, that the vulnerability of the IBM QRadar Wincollect ends when we delete the WER folder (or any other file/folder you want to delete).
The use of the arbitrary delete issues, in order to escalate to SYSTEM, is irrelevant to this vulnerability and it is an MS Windows issue. This technique has been described by Jonas L in his blogpost https://secret.club/2020/04/23/directory-deletion-shell.html
The delete.exe is an implementation of this technique, which can be found in my github repo https://github.com/DimopoulosElias/Primitives
Video PoC Step By Step
00:00-00:11: We present the environment. We are low privileged users and the installer file we are going to use is the 11ec43.msi . This file, belongs to IBM and is the installer file of the wincollect agent.
00:11-00:22: As low privileged users, we run the installer. At the end of this time frame (00:22) the wincollect service has stopped . We can stay at this position as long as we want to and perform any actions we want to, with the wincollect service being disabled (CVE-2020-4485).
00:22-00:58: We are going to use the technique presented by Jonas L , in order to leverage the arbitrary delete and gain access as SYSTEM. For this to be achieved, we need to delete the folder C:\ProgramData\Microsoft\Windows\WER , which can not be deleted by a low privileged user. However, some sub-folders can be deleted. At this time frame, we delete the sub-folders we are able to, without any exploitation.
00:58-02:42: By exploiting the CVE-2020-4486 , we delete the remaining files and sub-folders from the WER folder. A low privileged user, would not be able to delete those files/folders, as we presented in the previous time frame. The $INDEX_ALLOCATION is used in order to delete a folder instead of a file .
02:42-03:58: We run the exploitation procedure one more time, in order to delete the C:\ProgramData\Microsoft\Windows\WER folder. At this point, the use of CVE-2020-4486 ends. The rest of the video presents the use of this primitive in order to escalate to SYSTEM and is irrelevant to the IBM WinCollect issues.
03:58-end: Now that we have deleted the WER folder, we use the https://github.com/DimopoulosElias/Primitives is order to become a SYSTEM. Again, this has nothing to do with the IBM vulnerabilities. It’s a primitive which allows us to use any (or almost any) arbitrary delete, in order to escalate to SYSTEM.
We will leave the escalation with the use of symlinks as an exercise for you 🙂 .
Resources
GitHub
You can find our exploits code in our GitHub at https://github.com/RedyOpsResearchLabs/
RedyOps team
RedyOps team, uses the 0-day exploits produced by Research Labs, before vendor releases any patch. They use it in special engagements and only for specific customers.
You can find RedyOps team at https://redyops.com/
Angel
Discovered 0-days which affect marine sector, are being contacted with the Angel Team. ANGEL has been designed and developed to meet the unique and diverse requirements of the merchant marine sector. It secures the vessel’s business, IoT and crew networks by providing oversight, security threat alerting and control of the vessel’s entire network.
You can find Angel team at https://angelcyber.gr/
Illicium
Our 0-days cannot win Illicium. Today’s information technology landscape is threatened by modern adversary security attacks, including 0-day exploits, polymorphic malwares, APTs and targeted attacks. These threats cannot be identified and mitigated using classic detection and prevention technologies; they can mimic valid user activity, do not have a signature, and do not occur in patterns. In response to attackers’ evolution, defenders now have a new kind of weapon in their arsenal: Deception.
You can find Illicium team at https://deceivewithillicium.com/
Neutrify
Discovered 0-days are being contacted to the Neutrify team, in order to develop related detection rules. Neutrify is Neurosoft’s 24×7 Security Operations Center, completely dedicated to threats monitoring and attacks detection. Beyond just monitoring, Neutrify offers additional capabilities including advanced forensic analysis and malware reverse engineering to analyze incidents.
You can find Neutrify team at https://neurosoft.gr/contact/